Knowi uses single sign-on (SSO) for Enterprise users to simplify the sign-in process and allow access to Knowi using several authentication sources, including Okta. Your Workspace must be subscribed to the Enterprise plan if you wish to set up SSO.
If you're the Admin of your company's Enterprise account, you can configure SSO using the following steps:
-
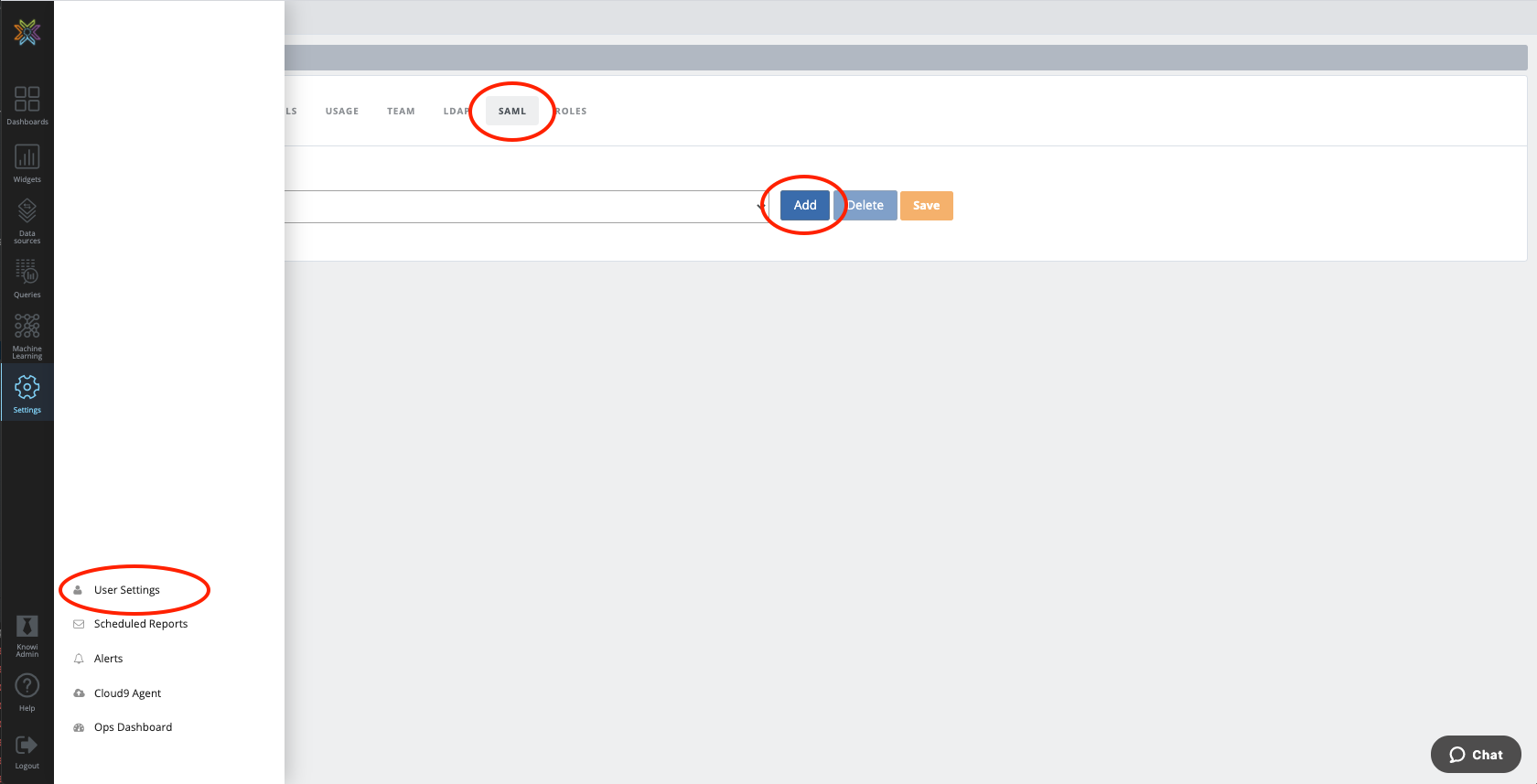
Go to your SAML tab by clicking on Settings in the left navigation bar then User settings. Click on SAML then Add. Keep this tab open, as you'll be returning to your Knowi Workspace later.
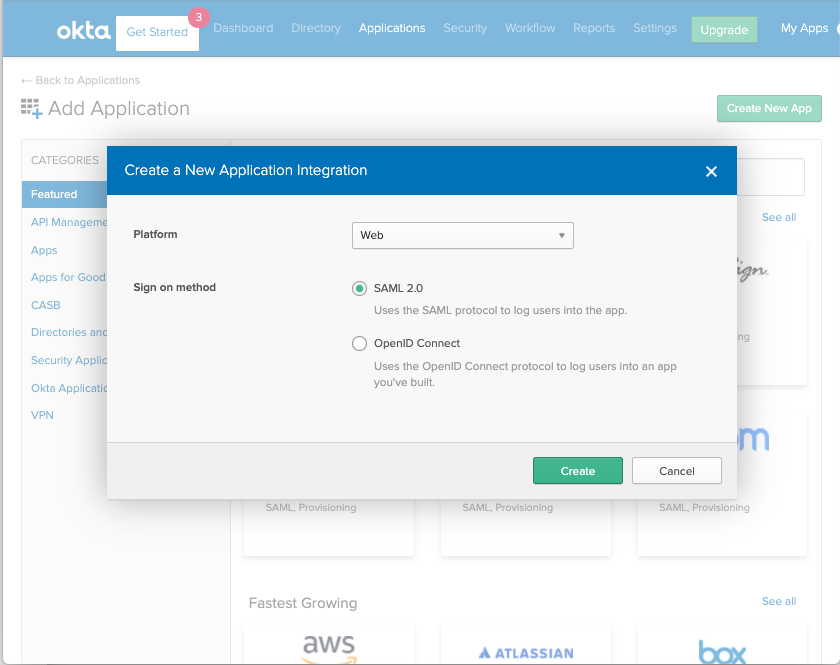
- Open up your Okta admin portal and set up a new application using the Applications tab. Select SAML 2.0 as your sign-on method. Configure your new integration by naming it Knowi and adding a logo if you want.
- You'll now see Knowi's SAML Settings. Start with the General section below. You'll need to grab some information from Knowi and input it into Okta:
• Paste the SSO URL from Knowi into the Single sign on URL field on Okta.
• Paste the Audience URI from Knowi into the Audience URI (SP Entity ID) field on Okta.
• For Name ID format, choose Unspecified.
• For Application username, choose Okta username.
- Scroll down to Attribute Statements in Okta. You'll need to map your fields:
• For userId, map to the value within your organization's Okta setup.
• For userEmail, map to the value within your organization in Okta. Note: It's important to follow the same capitalization format in your organization when you add this name.
• For userLogin, map to your organization's Okta value as well. Capitalization matters here, too.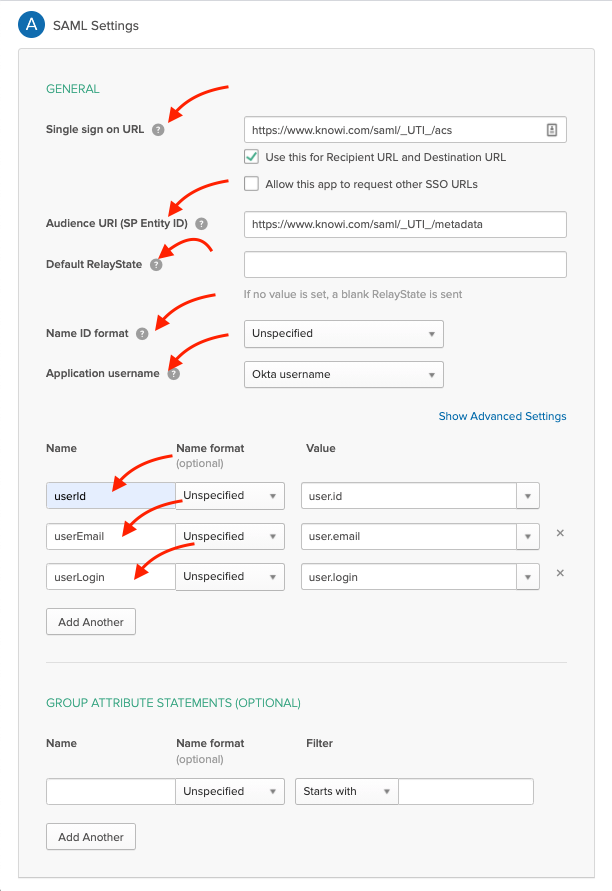
Knowi doesn't yet support group attribute statements, so you can leave that portion blank.
- Hit next and fill out the final Okta form according to your own preferences. This won't impact anything in your Knowi Workspace.
- Your application is ready! You'll now need to take some information from Okta and bring it back to your Knowi portal. Start by clicking View Setup Instructions in your Sign-on Methods settings.
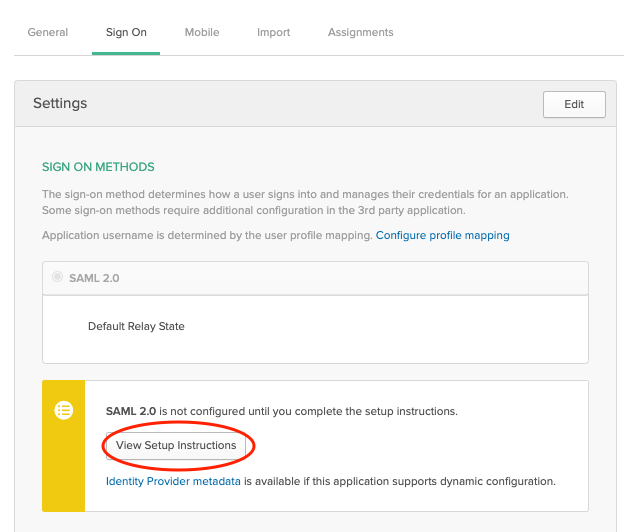
• Paste your IdP SSO URL under Identity Provider Single Sign-ON URL in your Knowi SAML settings where it says IdP URL.
• Paste your IdP Issuer under Identity Provider Issuer in your Knowi SAML settings where it says IdP Issuer.
• Copy and paste your X.509 Certificate from your setup instructions in Okta to your Knowi SAML settings.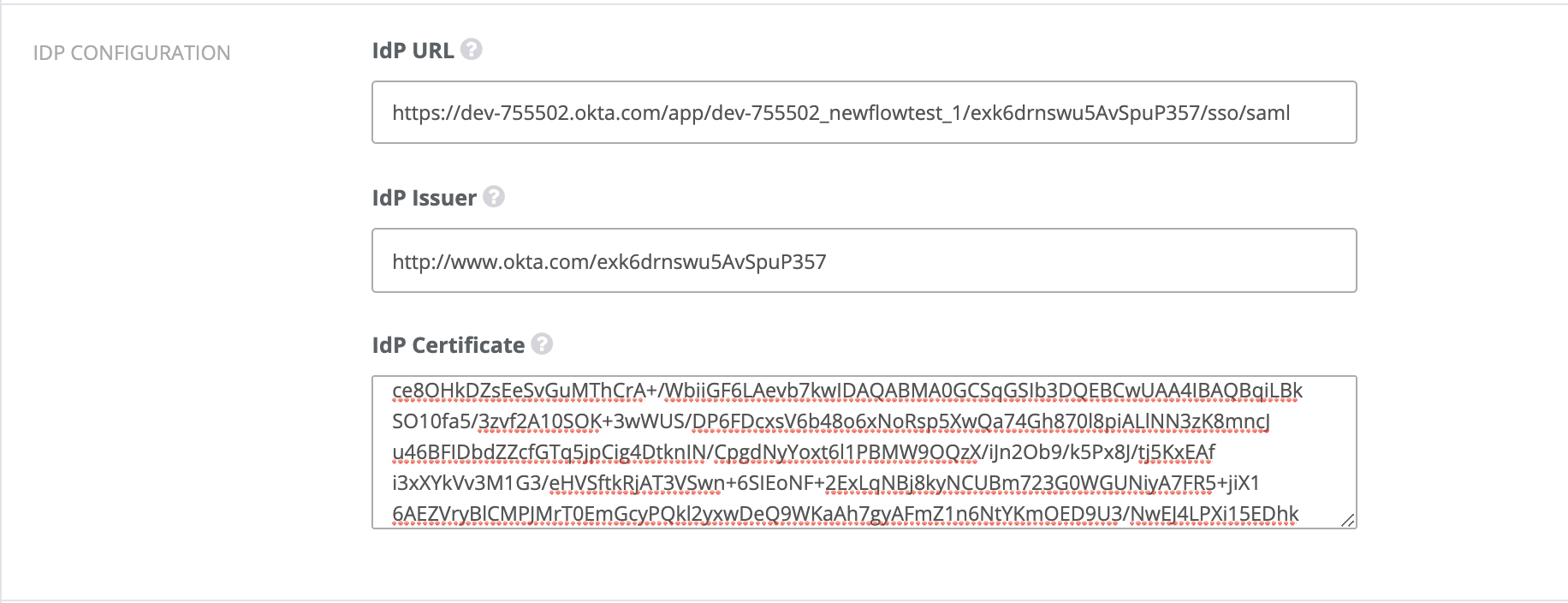
- You can Test configuration and Save the Knowi SAML settings.
Additional SAML attributes supported by Knowi
- contentFilter: The contentFilter attribute lets you set content filters for your users. Like all other attributes, it can be on groups or directly on a user within your IDP and they stack up like the 'group' attribute. Please note that it might be necessary to enable attribute aggregation on your IDP for stackable attributes. If no contentFilter attribute is present, content filters for that user will be unset, meaning the user has access to the full data.
- dashboardUrl: sets the dashboard that a user sees after logging in. You can either paste the entire URL or just the dashboard ID part from a URL, both should work. If this attribute is not present, the most recently opened dashboard will be displayed for return logins and the playground will be launched for new users.
- role: sets the user role, only one role per user is supported at this time. If no role is provided from an attribute, the default role from the SAML configuration will be used.
- groups: The groups that the user will be part of in Knowi. Users can be put into multiple groups in Knowi by adding more than one 'group' attribute. If no groups attribute is present, the default groups from your SAML config will be used.
- logoutUrl: this attribute, a full URL, for example, https://www.knowi.com will cause the user to be redirected to that URL upon logout. If this attribute is not set, the knowi home page will be opened upon logout.